Shell companies — legal entities with no substantial operations of their own — are a staple of legitimate corporate structuring. They are also among the most frequently abused instruments in financial crime, sanctions evasion, corruption, and money laundering. For compliance teams, investigators, and financial institutions, identifying and understanding a shell company's true nature is one of the most consequential tasks in modern due diligence.
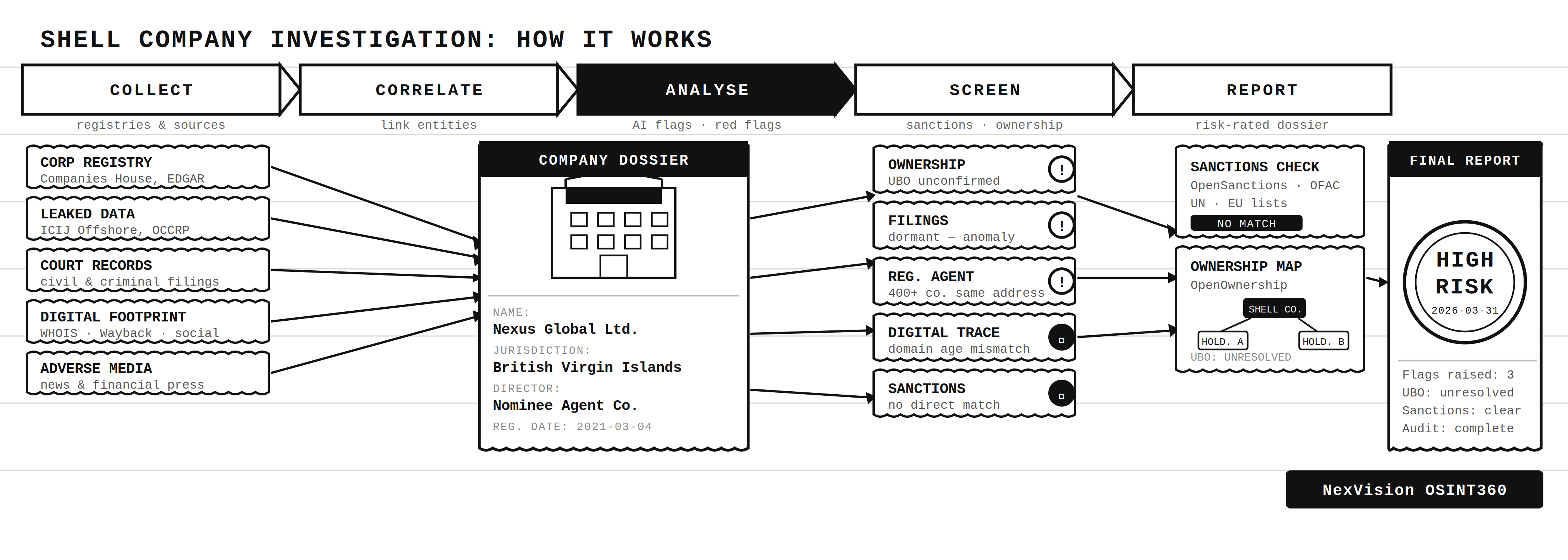
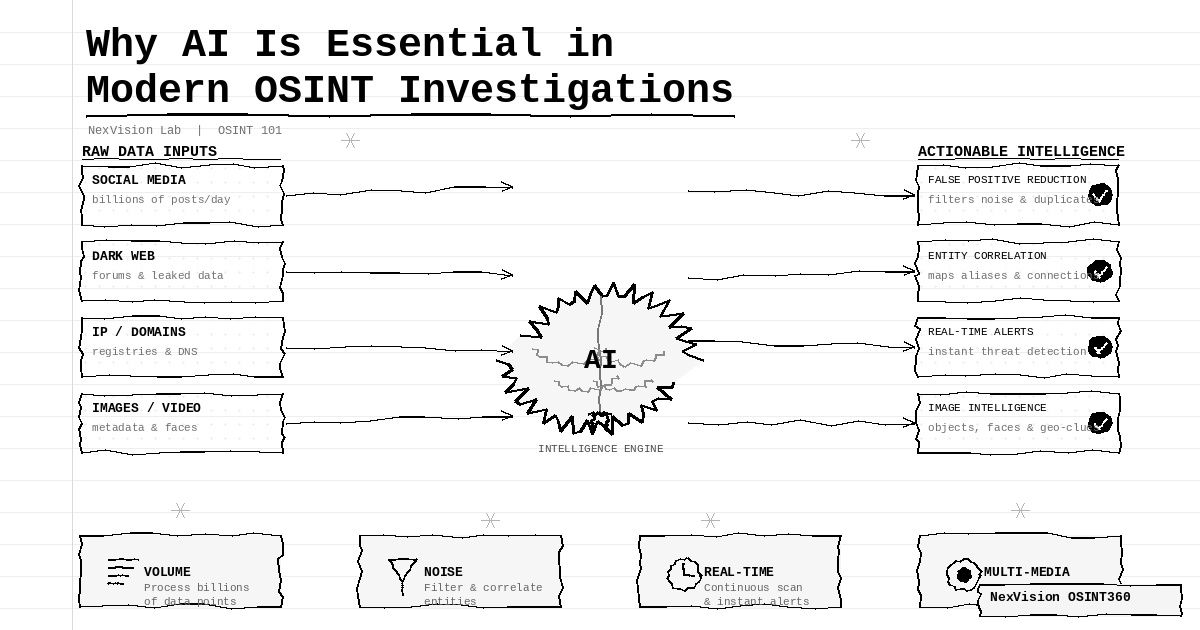
Open Source Intelligence (OSINT) offers a structured, lawful, and highly effective pathway to conduct this investigation. By systematically querying public registries, cross-referencing leaked data, analysing digital footprints, and mapping ownership structures, analysts can build a coherent picture of whether a corporate entity is genuine — or a vehicle for concealment.
This guide presents a complete end-to-end methodology for conducting OSINT-based corporate due diligence on a suspect shell company. Each phase builds on the last, and together they form an investigation workflow that is repeatable, defensible, and grounded in open-source data.
NexVision OSINT360
This investigation workflow is designed to be conducted using NexVision OSINT360 — a unified intelligence platform that aggregates corporate, financial, social, and technical data sources in a single environment, dramatically reducing the time and effort required at each step.
Access the NexVision OSINT360 platform →Understanding the Shell Company Problem
A shell company is, by definition, a company with no independent operations, assets, or employees of its own. Its legal existence may be entirely legitimate — holding companies, special purpose vehicles (SPVs), and personal asset holding structures are all common and legal uses. The problem arises when the corporate form is used to obscure beneficial ownership, distance assets from their true origin, or create a false impression of commercial activity.
"The challenge is not the structure itself, but what it hides. OSINT allows investigators to look past the corporate form and interrogate the substance behind it."
Common indicators of a suspect shell company include: incorporation in a secrecy jurisdiction with no apparent business operations there, nominee directors who appear on hundreds of company boards globally, registered addresses shared by dozens of unrelated entities, inconsistent or implausible financial filings, and an inability to identify a real beneficial owner.
OSINT does not prove criminal activity — it assembles evidence of opacity. The analyst's task is to determine whether that opacity is explainable and commercially rational, or whether it raises concerns that require escalation.
The Investigation Methodology
The following eleven steps constitute a comprehensive OSINT due diligence workflow. They are designed to be followed sequentially, as each phase enriches the data available for subsequent stages.
The foundation of any investigation is a complete and accurate target profile. Begin by documenting everything already known about the entity: the full legal company name (and any known trading names or abbreviations), registration numbers, the jurisdiction of incorporation, known physical addresses, and the names of any associated individuals — including directors, officers, shareholders, and registered agents. This initial data package anchors all subsequent searches and prevents scope drift.
Even imprecise information is valuable at this stage. A partial address, a former director's name, or an old registration number may unlock critical links as the investigation progresses. Record all variations and document the source of each data point from the outset.
With your target identifiers in hand, the next step is to consult official corporate registries. These are government-maintained databases that record the formal legal existence of companies — including their incorporation date, registered address, directors, and in some jurisdictions, financial filings.
Using the NexVision OSINT360 platform, you can query multiple registry sources simultaneously. Supplement this with direct searches of national and regional databases: in the UK, Companies House; in the US, SEC EDGAR for public companies and individual state secretaries of state for private entities; in the EU, the e-Justice portal for cross-border registry access. For international entities, OpenCorporates aggregates data from over 140 jurisdictions in a single searchable interface.
The goal at this stage is to confirm (or correct) the basic facts already gathered, and to begin identifying gaps — filings that should exist but do not, inconsistencies in declared addresses, or jurisdictions with no apparent commercial logic.
Corporate filings tell a story over time. A company's filing history — its annual accounts, confirmation statements, change notifications, and dormancy declarations — reveals whether it is behaving as a genuinely active commercial entity or as a dormant vehicle maintained for other purposes.
When reviewing filing history, look for: persistent dormancy declarations that coexist with apparent commercial activity; missed or significantly late filings; sudden unexplained changes in directors or registered address; share capital that is negligibly small (a single £1 share is a common signal); and accounts that show zero or negligible turnover despite the company claiming to operate in a high-value sector.
The registered agent — the individual or firm designated to receive official correspondence on behalf of the company — is often the only concrete link between a shell and the jurisdiction in which it is incorporated. Identifying and scrutinising this agent is therefore a critical step.
Using NexVision OSINT360 alongside standard search tools, query the registered agent's name and address across corporate databases. A key analytical technique is to cross-reference the physical address: if a single address is shared by dozens or hundreds of unrelated companies, it almost certainly belongs to a professional company formation service — a business that creates and maintains corporate shells for clients who wish to remain anonymous.
This in itself is not illegal. Professional formation agents operate legitimately in many jurisdictions. But the use of such an agent, particularly in a secrecy jurisdiction, is a strong indicator that the true beneficial owner is deliberately distancing themselves from the corporate record.
Several major investigative journalism projects have produced searchable databases of offshore financial data that are invaluable in corporate investigations. These include the Panama Papers, the Pandora Papers, the FinCEN Files, the Luanda Leaks, and others — all consolidated and searchable through the ICIJ Offshore Leaks Database.
Search for the company name, associated individuals, and the registered agent across these databases. A match does not automatically indicate wrongdoing — many legitimate companies appear in offshore data — but it provides important context and may reveal links to structures or individuals already under scrutiny.
The OCCRP Aleph platform offers a complementary search capability, aggregating court records, company registries, and investigative journalism datasets from across the world. Run your company name, directors, and addresses through both platforms before moving on.
Before any business relationship can be considered, a thorough sanctions check is mandatory. Screen the company name, all known directors and officers, beneficial owners, and associated addresses against major international sanctions and watchlist databases.
Key lists include: the US Office of Foreign Assets Control (OFAC) Specially Designated Nationals list, the UN Consolidated Sanctions List, EU and UK sanctions registers, and Interpol notices. OpenSanctions aggregates these sources into a single searchable interface and is a practical starting point. The NexVision OSINT360 platform integrates sanctions screening directly into the investigation workflow.
Note that sanctions screening extends beyond exact name matches. Ownership or control by a sanctioned individual — even if that individual is not named directly in the company record — may constitute a sanctions exposure. This is why the beneficial ownership mapping in the next step is so important.
The ultimate beneficial owner (UBO) is the natural person — or persons — who ultimately own or control the company, even if that ownership is exercised through layers of intermediate entities. Identifying the UBO is frequently the most challenging and consequential step in the due diligence process.
Begin with official UBO registers where available: the UK's Persons of Significant Control (PSC) register, accessible via Companies House, requires all companies to declare individuals who own more than 25% of shares or exercise significant influence or control. EU member states maintain similar registers under the Anti-Money Laundering Directives. OpenOwnership aggregates beneficial ownership data from multiple jurisdictions and is an essential resource.
Where official registers reveal only another company as the UBO (rather than a natural person), the investigation must continue up the corporate chain. Use NexVision OSINT360 and link-analysis methods to map the full ownership structure visually. Look for: circular ownership arrangements (where Company A owns Company B, which in turn owns Company A) — these are structurally impossible in legitimate corporate law and a clear signal of deliberate obfuscation.
Nominee arrangements — where an individual or company holds a directorship or shareholding on behalf of the real controller — are a cornerstone of shell company opacity. The nominee appears on the public record; the true controller does not.
Identifying nominees requires pattern recognition rather than a single database lookup. Cross-reference all named directors across company databases: a natural person who sits on the board of hundreds of companies across multiple jurisdictions is almost certainly providing nominee services professionally. Similarly, a shareholder that is itself a company registered in a secrecy jurisdiction with no public UBO record is a strong indicator of a nominee shareholding arrangement.
Document all relationships between the nominees found and other companies in which they appear. This network mapping frequently reveals connections between seemingly unrelated entities that share the same underlying controller.
Court records are among the richest and most underutilised sources in corporate intelligence. Civil litigation, enforcement actions, bankruptcy filings, and criminal proceedings involving either the company or its associated individuals can reveal a pattern of behaviour that no corporate registry will disclose.
Search for the company name and all known director names through publicly accessible court portals. In the UK, the HMCTS Find Case Information service provides public access to civil court records. In the US, PACER provides access to federal court filings, while CourtListener offers free access to a substantial archive of federal and state decisions. Many jurisdictions in Europe and beyond maintain their own public court registries.
Pay particular attention to: judgments for debt recovery; allegations of fraud or misrepresentation in commercial proceedings; insolvency actions; regulatory enforcement notices; and any mention in proceedings involving sanctioned individuals or criminal networks.
Structured databases and official registries capture what companies disclose. Adverse media search captures what journalists, regulators, and whistleblowers have reported — often revealing information that never appears in any official record.
Conduct systematic searches across international news archives for the company name, its directors, its registered address, and its associated individuals. Look for: coverage of fraud investigations or allegations; regulatory censure; association with known criminal networks; bankruptcy or asset seizure reporting; or appearance in investigative journalism connected to financial crime.
Commercial adverse media platforms provide structured, deduplicated searches across global news sources with risk categorisation. For OSINT-based investigations, Google News, OCCRP's Aleph, and thorough Boolean search strategies across major news databases are effective and accessible alternatives.
A company's digital infrastructure — or its conspicuous absence — tells its own story. This phase examines the online presence of the entity through domain analysis, contact data, web archive research, and social media investigation.
Domain and WHOIS analysis: Identify any website associated with the company and run a WHOIS query to retrieve domain registration details: registrant name, organisation, email, registration date, and hosting provider. A domain created weeks before a major contract was signed — or a registrant using a privacy proxy — warrants close scrutiny. Compare the domain registration date against the company's claimed founding date.
Contact data extraction: Attempt to identify phone numbers and email addresses associated with the company from its website, public directories, and business listings. Verify whether these are real points of contact or disposable forwarding addresses. The NexVision OSINT360 platform can assist in correlating contact data with other known entities.
Web archive research: Use the Wayback Machine to review the historical development of the company's website. A company that claims to have been operating since 2015 but whose website has no archived versions prior to 2023 has a credibility problem that requires explanation.
Social media footprint: Search for the company across LinkedIn, Facebook, X (formerly Twitter), Instagram, and regional platforms. A genuine commercial entity will typically have some employee presence, a verifiable company page, and engagement consistent with its claimed activity. An absence of any meaningful social presence — particularly for a company claiming significant operations — is a red flag.
Advanced search techniques: Apply Google Dork operators to surface information that standard searches miss. Search the company name in quotes, combined with terms such as "invoice," "contract," "agreement," "complaint," or "fraud." Search the registered address in quotes to identify all other companies sharing that address. These techniques frequently yield documents, reports, and references that shed new light on the entity's true activities.
Assigning a Risk Rating and Producing the Report
With the investigation complete, the final step is to consolidate all findings into a structured due diligence report with a defensible risk rating. Every conclusion must be grounded in a specific, citable source — and the distinction between confirmed facts, strong indicators, and unverified leads must be explicit throughout.
A useful four-tier risk framework is as follows:
| Rating | Criteria | Recommended Action |
|---|---|---|
| Low | No red flags identified. Corporate structure is transparent and commercially rational. UBO confirmed. | Proceed with standard monitoring. |
| Medium | Some unexplained elements (e.g. nominee directors, offshore jurisdiction) but no confirmed adverse findings. | Proceed with enhanced due diligence and periodic review. |
| High | Multiple red flags: UBO unconfirmed, adverse media present, filing anomalies, or appearance in investigative databases. | Do not proceed without further verification. Escalate to compliance and legal. |
| Critical | Confirmed sanctions match, PEP association with unresolved concerns, or confirmed fraud/criminal nexus. | Hard stop. Escalate immediately. Consider regulatory reporting obligations. |
The final report should follow a consistent structure: an executive summary with the risk rating prominently stated; an entity overview drawing on registry data; a corporate structure and ownership map; a summary of all adverse findings; and a full source appendix with URLs, access dates, and archive links. Every data point should be datestamped — corporate information changes, and a report is only as reliable as its sources.
A Note on Ethical and Legal Boundaries
OSINT-based due diligence must operate entirely within the bounds of publicly available, lawfully accessible information. The discipline's strength — and its legal legitimacy — rests on the fact that every data point is drawn from open sources that anyone could access. This means no social engineering, no accessing private systems, no purchasing data from unlawful brokers, and no retention of personal data beyond the scope and duration justified by the investigation's purpose.
Investigators should also be mindful of data protection obligations. Personal data gathered about company directors and associated individuals during due diligence is subject to GDPR in the UK and EU and equivalent legislation in other jurisdictions. A clear lawful basis — typically legitimate interest — must be documented, and data must be handled proportionately and securely.
Finally, maintain a full and auditable record of every source consulted during the investigation. This documentation is essential if findings are ever challenged, disclosed to regulators, or relied upon in legal proceedings.